Why Security Teams Need the Scantist Expertise

Stay Ahead of Threats
Identify and remediate vulnerabilities early in development, preventing security risks from reaching production.
Swift Security Issue Remediation
Resolve security issues in real-time, enhancing productivity and minimizing security risks during development.
Comprehensive Reporting
Generate comprehensive reports to demonstrate compliance efforts, facilitating legal oversight and decision-making.
Scantist Process
Scan Activation
Scantist collects vital security-relevant information from your development landscape, such as build logs, codebases, and manifest files. This information is then securely transmitted to Scantist's central server for in-depth scrutiny.
Security Risk Assessment
Utilizing heuristic methods and machine learning, Scantist performs a thorough security analysis against a specialized vulnerability database. This identifies a wide range of vulnerabilities - from CVEs and vulnerable open-source vulnerabilities, to OWASP Top 10 issues, to runtime memory unsafe operations.
Results Availability
After analysis, Scantist makes the security assessment findings accessible via a specialized portal and API. These results can also be integrated seamlessly into your existing security tools and issue tracking systems for streamlined vulnerability management. The results can also be exported in human and machine readable formats.
Continuous Monitoring and Support
Continuous monitoring for fresh vulnerabilities and potential risks, to offers prompt support to maintain software's security strength, ensuring protection from evolving threats.
Business Impacts
Translating risk mitigation to business success.
Visibility and Transparency
Accelerate time-to-market with faster development by enabling the use of open source components freely.

Reduce Risk of Data Breach
An average data-breach costs US$ 3.86 million globally. By eliminating open-source related vulnerabilities, organizations using reduce their risk of data breach from 32% to 24% - an average annualized saving of US$ 310,000.
Reduced Remediation Time
An 85% reduction in time and effort required to fix vulnerabilities can be achieved with the targeted remediation and recommendations in this report.
Compliance and Risk Management
Overall Improved license compliance and risk management with regards to open-source use, combined with an additional layer of defensibility.
Critical & Non-Critical Recommendations
Efficient use of security resources reduces security and compliance efforts, thereby lowering vulnerability management costs.

Empowering Security teams for Streamlined Software Security
Streamline processes, automate checks, and ensure codebase transparency to confidently navigate the legal landscape.
Multilingual Compatibility
From Java and JavaScript to Python and Ruby, we've got your software security covered, regardless of your preferred coding language.
Rapid Vulnerability Remediation
Swiftly identify and address security issues. This reduces the time it takes to resolve vulnerabilities, minimizing exposure and potential damage.
Multiple deployment solutions
Select from managed cloud, private cloud, or on-premise solutions, ensuring flexibility and customization to match your unique requirements.
Upskill your team with the skills they need



CCP for DevSecOps
Empower your organisation’s Professionals, Managers, Executives and Technicians (PMETs) with the skills needed for successful career conversion into new, promising high-growth and strong career prospects.

NTU - Scantist DevSecOps Professional & Tools
Gain a deep understanding of DevSecOps, get hands-on experience with key tools, and the leadership skills to drive security improvements in software development. An upskill program for DevOps professionals and those transitioning to the field.
Resources
Find out how we’ve helped organisations like you.

PAIStrike vs. DVWA - A Technical Deep Dive into Autonomous Attack Chains
In Part 1 of our series, we introduced the results of PAIStrike’s controlled benchmark against the Damn Vulnerable Web Application (DVWA), where it identified 18 high-confidence vulnerabilities. But the real story isn’t just the number of findings—it’s how they were discovered.
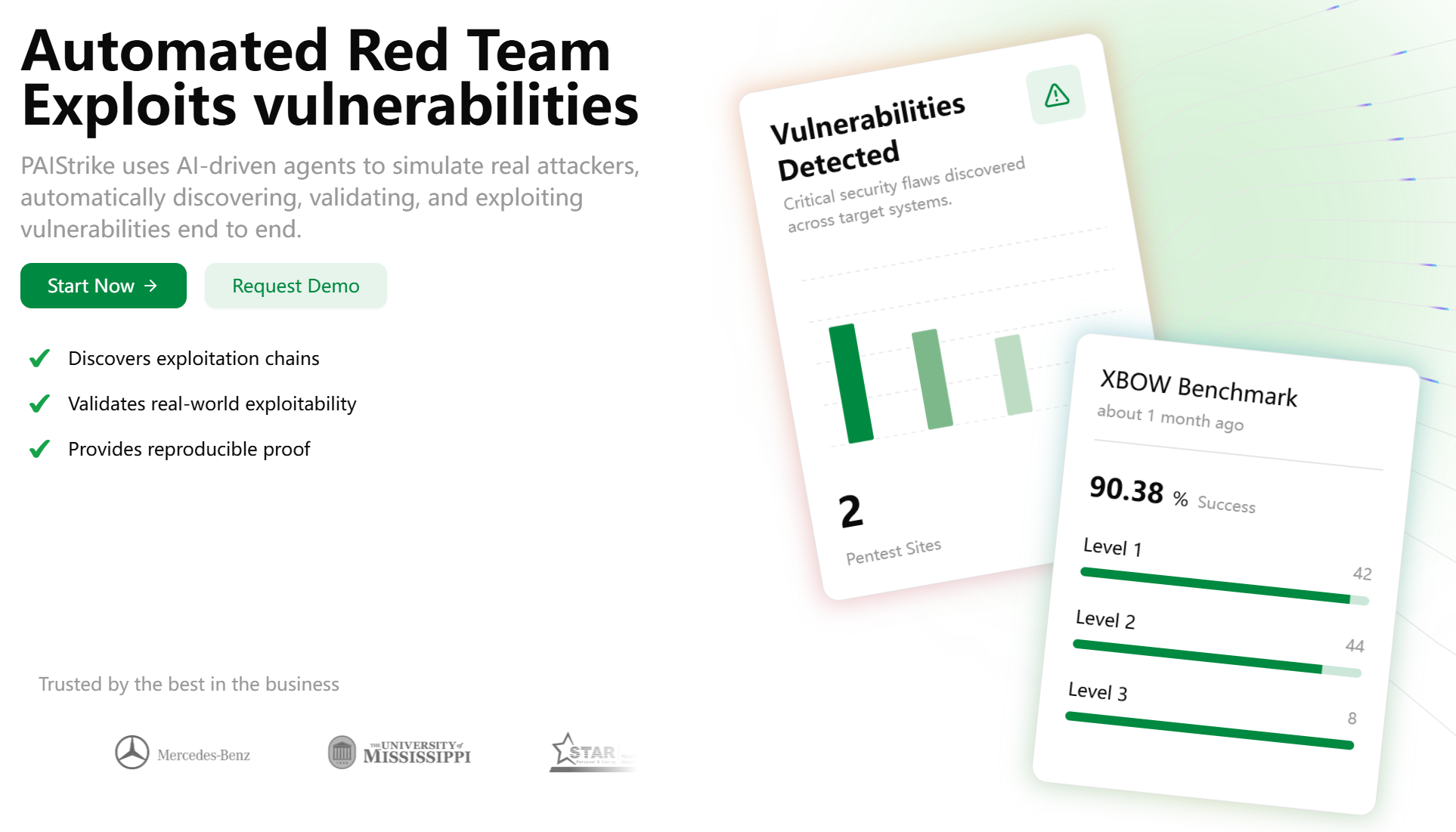
PAIStrike vs. DVWA - A New Benchmark for Autonomous Security Validation
This document contains a 3-part blog series rewriting the DVWA benchmark showcase based on the new validation report, complete with corresponding social media posts.
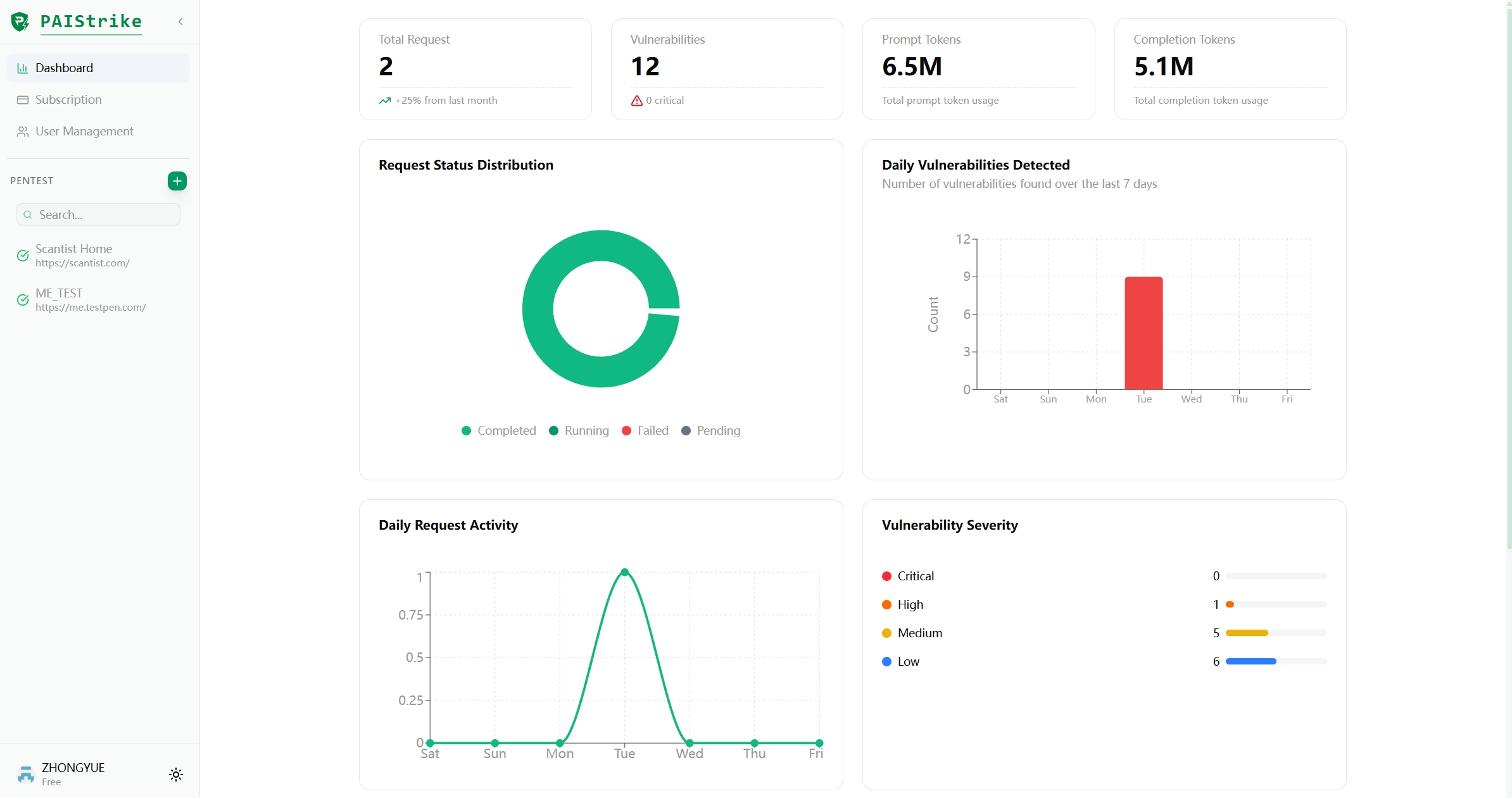
Redefining Automated Pentesting: PAIStrike Achieves L3 Capability with 100% Success on Stateful Attacks
PAIStrike is proud to answer that call with the results of its latest engine optimization on the rigorous, public XBEN benchmark. These results not only validate PAIStrike's performance but signal a fundamental shift in the maturity of automated penetration testing, confirming our transition to a true Stateful Automated Attack Engine.

Safeguard Your Source Code and Business
Join thousands of innovators, developers and security teams who trust Scantist to safeguard their software.
FAQs
Frequently Asked Questions (FAQ)
At Scantist, our advanced threat detection system employs a multi-layered approach to identify and neutralise potential security threats. We utilise a combination of machine learning algorithms, behavioural analysis, and signature-based detection to monitor your applications, libraries, and code repositories. Our system continuously scans for known vulnerabilities, suspicious patterns, and anomalous behavior, ensuring proactive threat mitigation and reducing the risk of cyberattacks.
We prioritise the security of your sensitive data and employ robust encryption standards. Scantist employs industry-leading encryption protocols, including TLS (Transport Layer Security), to secure data transmission between your systems and our platform. Additionally, all stored data is encrypted using strong encryption algorithms to prevent unauthorised access.
Yes, our identity and access management solutions are designed to seamlessly integrate with your existing systems. Scantist offers flexible integration options, including support for Single Sign-On (SSO) protocols such as SAML and OAuth. This enables you to centralise user authentication and access control, streamlining user management across your organization.
Our security consulting services provide expert guidance to identify, assess, and mitigate potential security risks within your software development lifecycle. Our team of experienced professionals can perform thorough security assessments, code reviews, and architecture analysis to pinpoint vulnerabilities and recommend effective risk mitigation strategies. By leveraging our consulting services, you can enhance your overall security posture and ensure the integrity of your applications.
Yes, we understand the importance of timely support, especially during emergencies and security incidents. Scantist offers customer support to address any urgent concerns you may have. Our dedicated support team is available to assist you in resolving issues, providing guidance, and ensuring a swift response to security incidents, helping you minimise potential impacts on your systems and operations.


