Why Choose Career Conversion Programs
with Scantist
Expert-Led
Curriculum
Learn from industry leaders with Scantist's curriculum, gaining insights from seasoned professionals.
Hands-on
Practical
Training
Acquire real-world skills through Scantist's immersive training, ensuring you're job-ready from day one.
Globally
Recognized
Certification
Earn a certification that's globally respected, opening doors to career opportunities worldwide with Scantist.
The Career Conversion Programs
Play a pivotal role in shaping the future of cyber security with career conversion programs in DevSecOps.
NTU Scantist DevSecOps Professionals & Tools Course
Lead DevSecOps initiatives within your organisation as you get hands-on in over half-dozen state-of-the-art tools that are essential to architecting DevSecOps pipelines.
Resources
Find out how we’ve helped organisations like you.

PAIStrike vs. DVWA - A Technical Deep Dive into Autonomous Attack Chains
In Part 1 of our series, we introduced the results of PAIStrike’s controlled benchmark against the Damn Vulnerable Web Application (DVWA), where it identified 18 high-confidence vulnerabilities. But the real story isn’t just the number of findings—it’s how they were discovered.
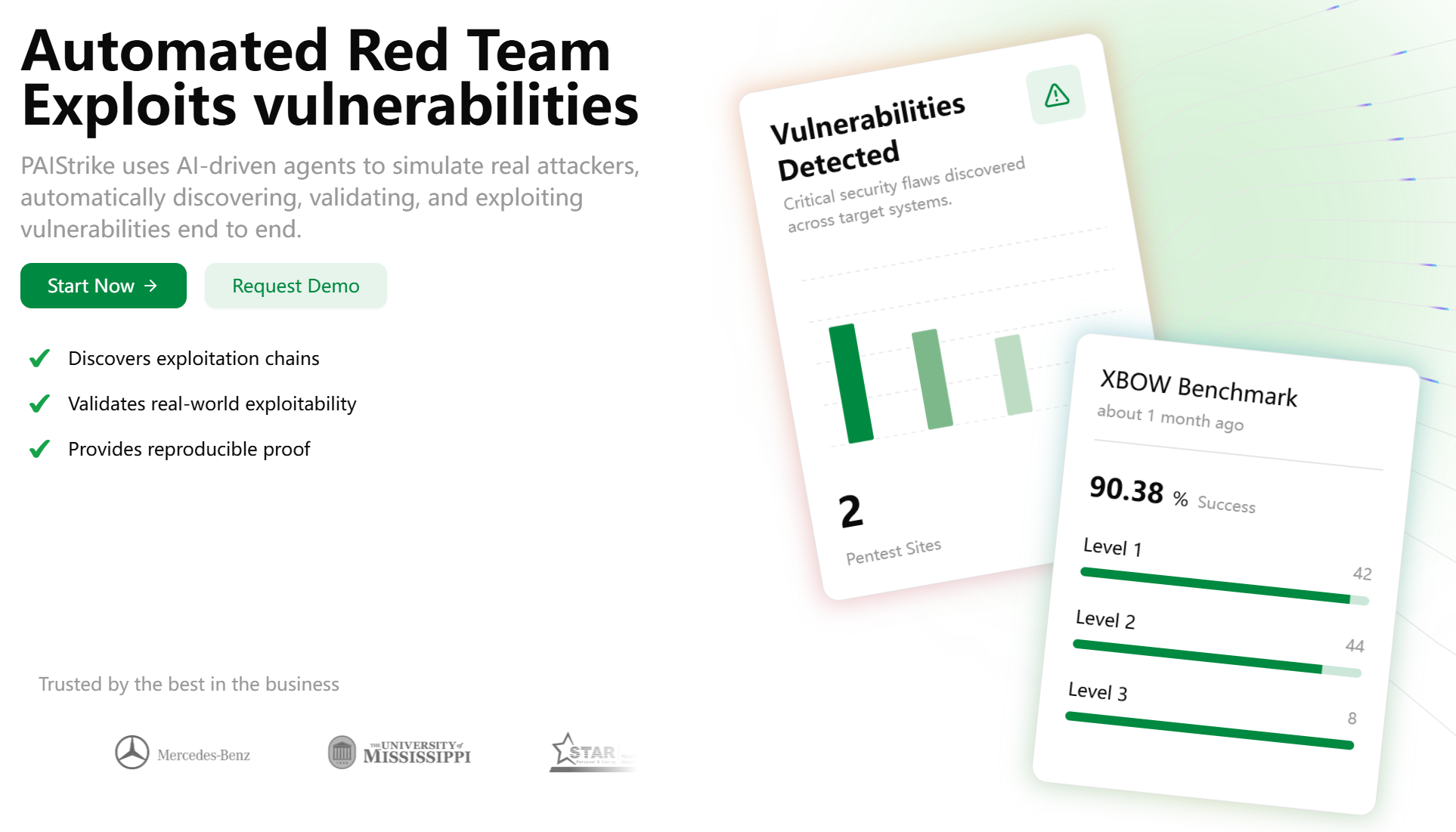
PAIStrike vs. DVWA - A New Benchmark for Autonomous Security Validation
This document contains a 3-part blog series rewriting the DVWA benchmark showcase based on the new validation report, complete with corresponding social media posts.
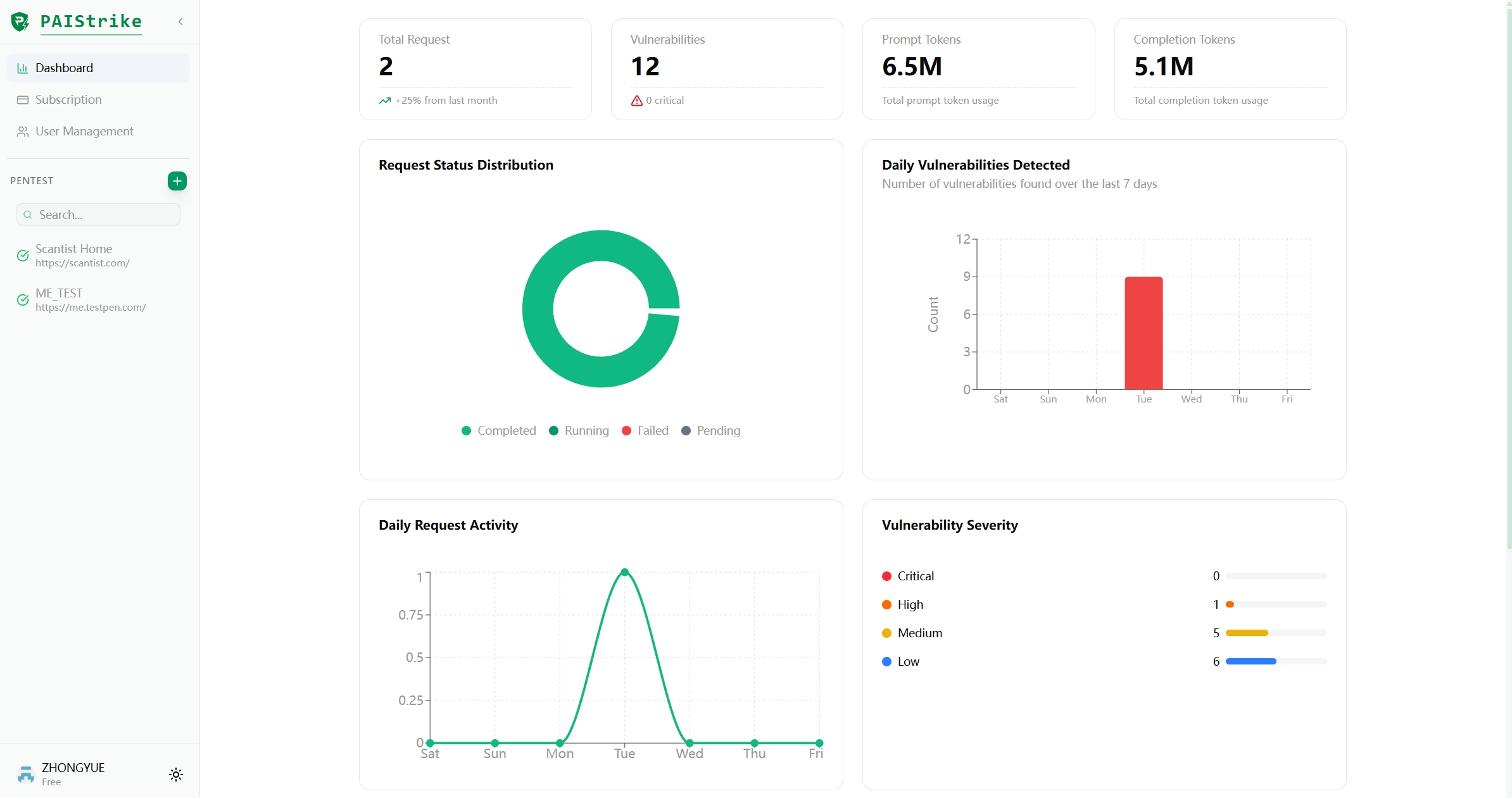
Redefining Automated Pentesting: PAIStrike Achieves L3 Capability with 100% Success on Stateful Attacks
PAIStrike is proud to answer that call with the results of its latest engine optimization on the rigorous, public XBEN benchmark. These results not only validate PAIStrike's performance but signal a fundamental shift in the maturity of automated penetration testing, confirming our transition to a true Stateful Automated Attack Engine.


