By PAIStrike Research Team, Scantist | March 2026
Security teams run penetration tests. They deploy vulnerability scanners. They manage bug bounty programs and run red team exercises. These are the right things to do.
And yet there is an entire category of risk that almost all of these approaches systematically miss — not because the tools aren't good enough, but because the assets are never on the list to begin with.
Ghost Asset (n.): Any digital infrastructure that is live, accessible, and handling real data — but has never been formally acknowledged, inventoried, or secured by the organization that owns it.
Ghost assets aren't vulnerabilities. They are the condition that makes vulnerabilities invisible. They don't appear in your asset register, your penetration test scope, or your monitoring alerts. They have no owner, no security review, and no one responsible for them.
But they're online right now — processing requests, storing data, and waiting.
Organizations generate ghost assets continuously through four primary channels:
1. Legacy InfrastructureA product feature gets deprecated. The API behind it doesn't. No one decommissions it, and it keeps running indefinitely — with no oversight, no patching, and no monitoring.
2. Frontend DependenciesModern web applications quietly depend on dozens of backend services. Most asset inventories capture the main domain — few capture every service that main domain calls on every user interaction.
3. AcquisitionsWhen you acquire a company, you inherit its entire infrastructure. Acquired services often run in production for months or years before security integration is complete — if it ever is.
4. Shadow ITServices deployed by business or engineering teams without security team involvement. Widespread in most enterprises. Carry essentially zero security coverage from day one.
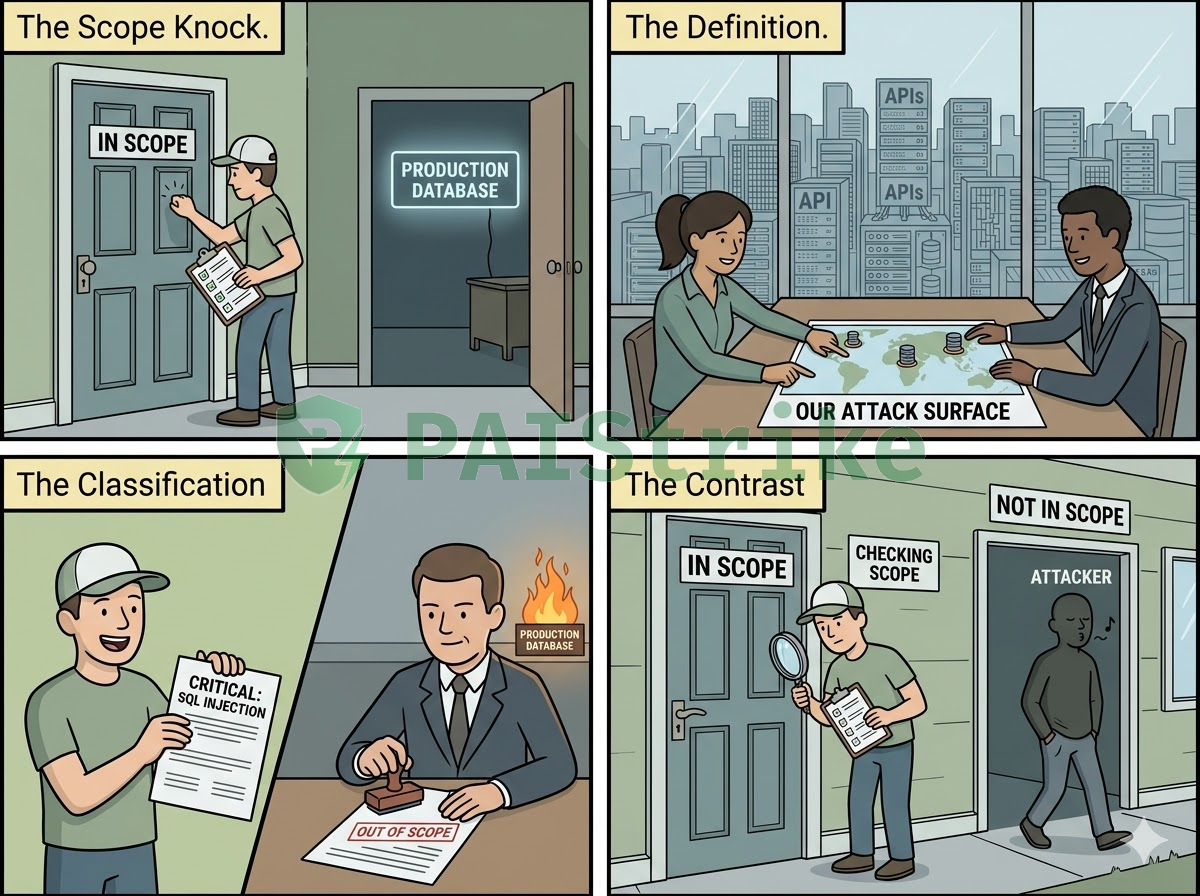
A security research team recently conducted an assessment of a platform running an active bug bounty program with a clearly defined scope. The scope was explicit: specific domains were in, everything else was out.
During the assessment, PAIStrike surfaced an API endpoint that wasn't listed anywhere in the program's scope documentation. The endpoint had no public documentation, no entry in the asset inventory, and no security coverage. But the platform's own frontend was calling it continuously — every time a user performed a standard product action.
This is the defining characteristic of a ghost asset: the organization's own production systems depend on it daily, but the security team has no record that it exists.
The attack path that emerged was straightforward — and devastating:
•In-scope frontend application (known, documented, monitored)
•→ Standard user interaction triggers an API call
•→ Undocumented backend API endpoint (unknown, uninventoried, out of scope)
•→ SQL injection in the countryCode parameter — POST body bypasses the cloud WAF
•→ Full production database access: 41,075 users · 41,000+ plaintext OAuth tokens · 1.2 million GPS records · financial data · 5 super admin accounts
From an attacker's perspective, this is a single, continuous path. The scope boundary doesn't appear anywhere on it.

PAIStrike's complete assessment identified 23 security vulnerabilities, including 5 rated Critical. Every single critical finding originated from infrastructure that was outside the defined bug bounty scope.
Critical #1 — Authentication Logic Flaw (Non-Expiring Sessions)Broken token refresh logic allows any valid session UUID to be reused indefinitely. Sessions never expire, enabling persistent unauthorized access.
Critical #2 — Broken Function-Level AuthorizationAny authenticated user can modify another user's payment settings. No ownership validation is performed on sensitive financial operations.
Critical #3 — Broken Object-Level AuthorizationAny authenticated user can permanently delete another user's GPS data. No resource ownership check is enforced on destructive operations.
Critical #4 — SQL Injection: Full Database Extraction152 tables exposed. 41,000+ user records, 41,000+ plaintext OAuth tokens, 1.2 million GPS sequences, financial data, and 5 super admin accounts fully accessible.
Critical #5 — Unauthenticated Access to Private User DataA photo endpoint requires zero authentication and serves private user images along with their precise GPS coordinates to any unauthenticated requester.
Plus 9 High severity findings — including global CORS misconfiguration, plaintext API secrets exposed in the public frontend bundle, and unauthenticated user database enumeration with no rate limiting.
The majority of these findings existed on infrastructure that was explicitly outside the bug bounty program's defined scope. Outside the scope — but not outside the attack surface.
This is not a tooling problem. It is a methodology problem rooted in a shared foundational assumption that every traditional security approach makes:
Vulnerability Scanners — Scan the targets you provide. Assets not on the input list are never scanned, regardless of how critical they are. → Blind spot.
Penetration Tests — Operate within a client-defined scope. Out-of-scope assets are excluded by contract and professional obligation. → Blind spot.
Bug Bounty Programs — Crowdsourced testing with the same dependency on scope definition. Financial incentives only apply to in-scope findings. → Blind spot.
All three methods share one foundational assumption: the organization knows what it has.
Ghost assets are precisely what organizations don't know they have. Any security approach that starts from an asset list will have systematic blind spots wherever that list is incomplete. And the list is always incomplete.
PAIStrike approaches this differently. Rather than starting from a provided asset list, it begins from the attacker's perspective — enumerating the real attack surface by following actual application behavior, tracing every call the frontend makes, and discovering infrastructure that exists in production but nowhere in any security document.
If you are responsible for security at your organization, these questions are worth sitting with honestly. The ones you cannot answer confidently are where ghost assets tend to live.
•When was your asset inventory last updated, and who owns the process of keeping it current?
•Does your inventory include every API endpoint your frontend applications call? Have you verified this empirically, or are you assuming?
•In the past two years, have you acquired companies or integrated third-party services? Has the security posture of those inherited assets been formally assessed?
•Who defines the scope of your penetration tests — your security team, or your business stakeholders? Are they working from the same picture of your infrastructure?
•If an attacker began enumerating your attack surface today, what would they find that your security team has never looked at?
Security isn't just about fixing known vulnerabilities. It starts with seeing your own system clearly.
PAIStrike starts from zero — just like an attacker. It discovers ghost assets, traces real application behavior, and validates the complete attack chain end-to-end. No scope document required.
Ready to find what your current tools are missing?
👉 Request a free PAIStrike trial: https://calendar.app.google/g4hV8dXQSHyEF4yCA
👉 Learn more about PAIStrike: https://scantist.com/paistrike
Case study data has been anonymized and redacted to protect the affected organization. Security assessment conducted by PAIStrike. March 2026.